Saratoga hub
Last updated April 8, 2019 by Brian
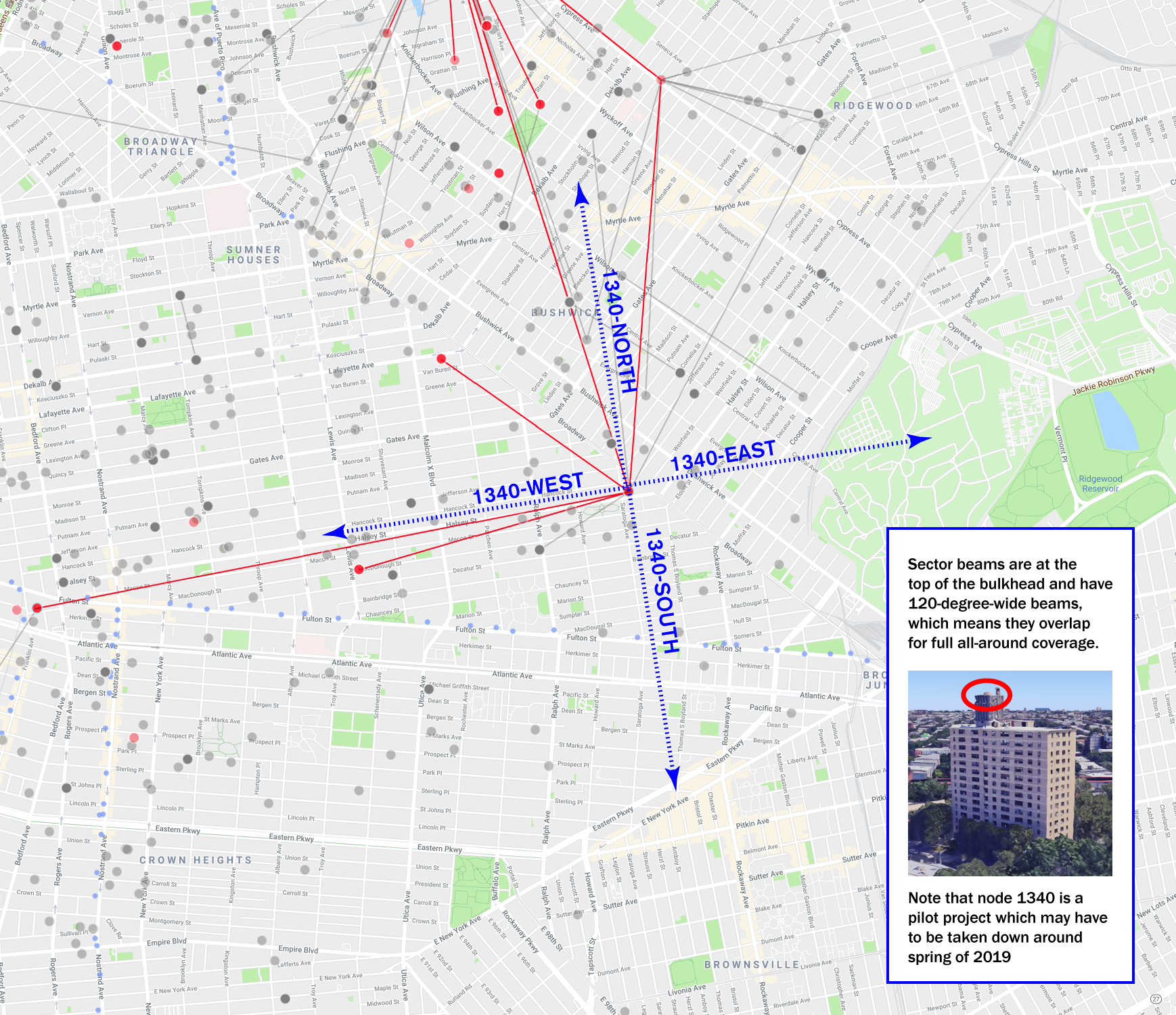
Saratoga hub (1340) is a hub node located at 33 Saratoga Avenue in Brooklyn New York. The installation provides mesh and internet connectivity for building residents as well as large areas of the Bedford Stuyvesant and Bushwick neighborhoods.

Status
https://stats.1340.nycmesh.net
Coverage
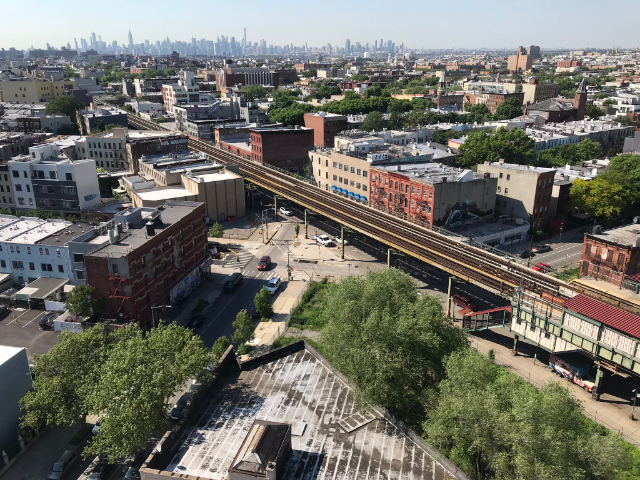
Photos

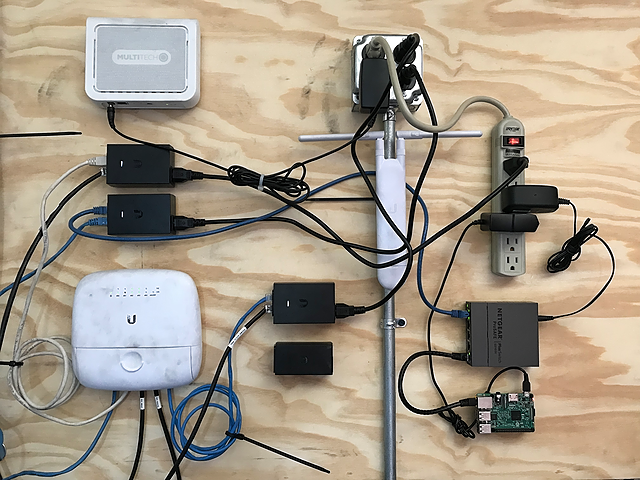

Hardware
| Description | Model | Manufacturer | Quantity |
|---|---|---|---|
| Router | EdgePointR6 | UBNT | 1 |
| Switch | EdgePointR6 | UBNT | 2 |
| Indoor AP | UniFi Mesh | UBNT | 5 |
| Powerline adapter | AV2000 (2-port Gigabit) | TP-LINK | 4 |
| Outdoor AP | SXT | Mikrotik | 1 |
| Outdoor AP | Nanostation M5 | UBNT | 1 |
| Wide area AP | LiteAP 120 | UBNT | 4 |
| Wide area station | Litebeam AC | UBNT | 2 |
| Application server | Raspberry Pi | RPi Foundation | 1 |
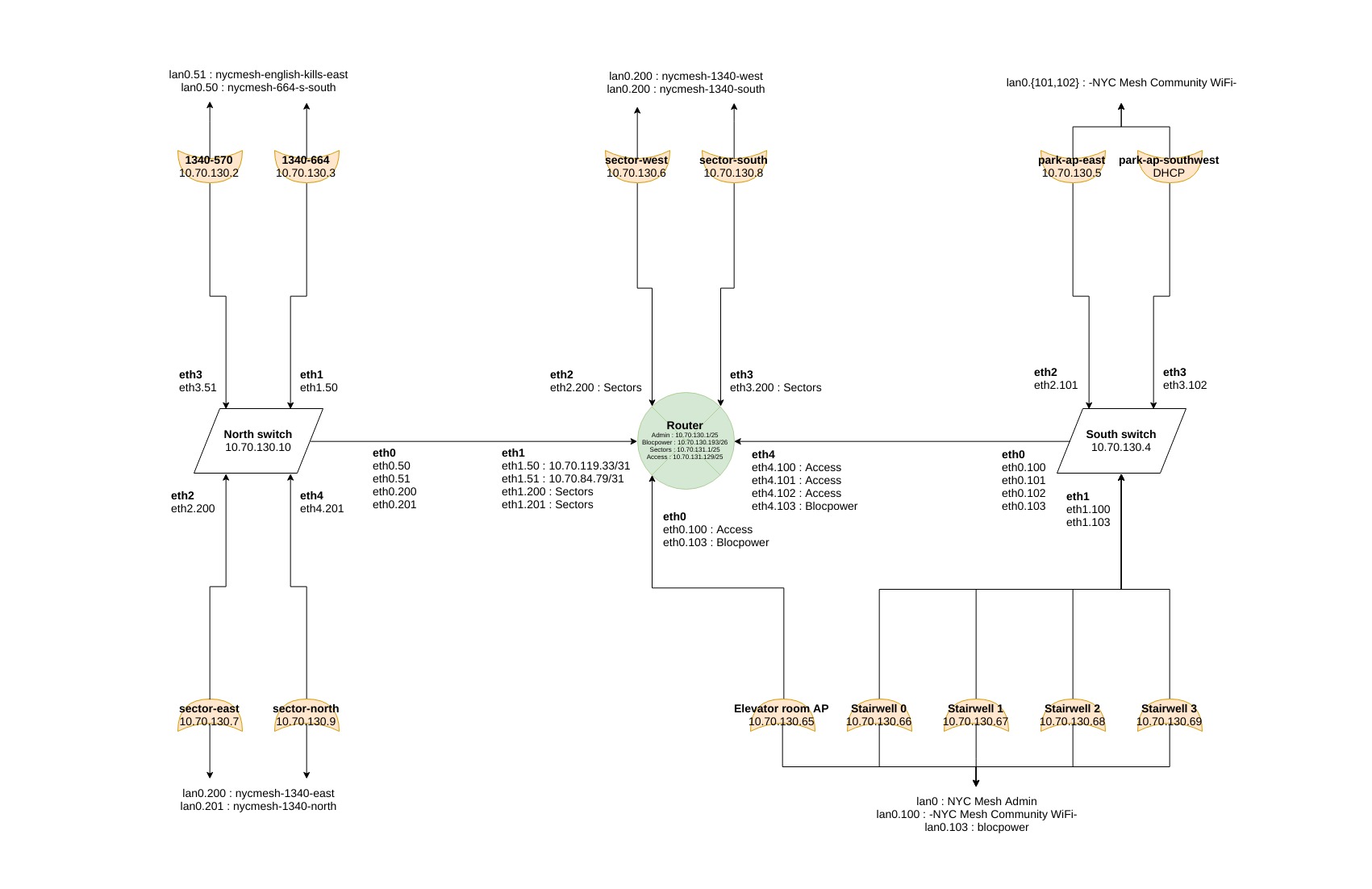
Schematic
Ethernet over power
We needed to place wireless access points deep inside the building but did not have permission or budget to run new conduit. We tried at first to backhaul the APs using a wireless mesh approach, but found the concrete walls and floors to be too thick to get acceptable performance. Ethernet and DC power are commonly multiplexed (called PoE or power-over-ethernet), but it’s also possible to multiplex ethernet and AC power. This was the technique we settled on as it utilized a pre-existing infrastructure and was able to deliver 100Mbps+ to each of our APs.

AP enclosures
The combination of an access point, PoE injector and EoP adapter resulted a somewhat awkward and exposed deployment - to protect them from damage and improve their appearance, our team designed custom 3d-printed enclosures:



Mounting
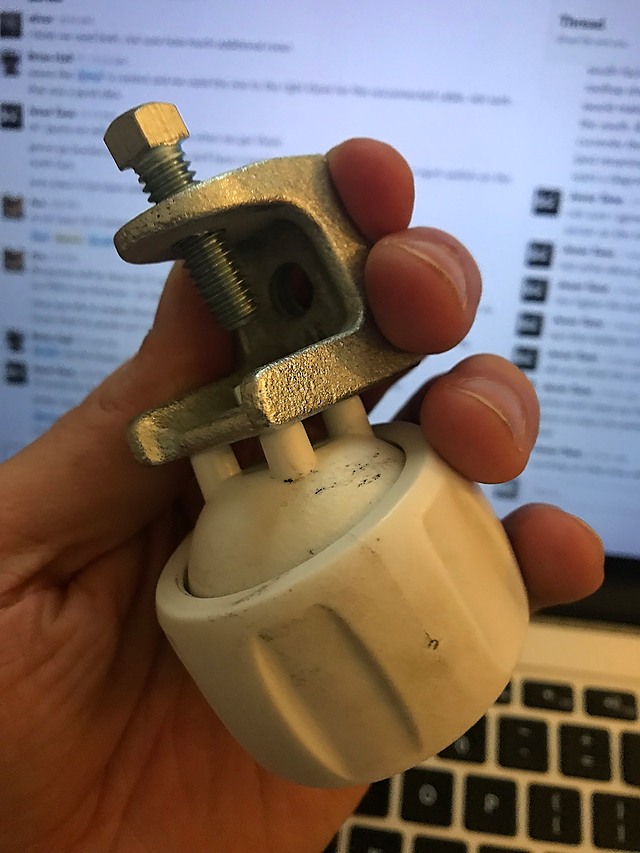
The mounting brackets shipping with the wide-area access points we deployed at the site are designed to clamp to poles. Unfortunately no appropriate structures predated our installation and given its potentially short term nature we devised a customized non-pentrating bracket using only readily available components from a local industrial electrical supplier.
Routing
1340 currently uses BGP to exchange routes with its mesh peers. We hope to upgrade this node to support additional dynamic routing protocols soon.
Switching
1340 enforces isolation at layer 2 on its public access networks for security reasons. The EP-R6 devices we had on hand have dedicated switching hardware (which is a nice thing) however no controls are exposed that provide a way to isolate ports in the traditional way. To achieve the desired effect we used VLANs to pass each wireless AP’s access net though to a linux bridge on the router. This has the unfortunate side effect of causing the router to send multiple identical copies of its broadcast frames over our trunk links, but fortunately the volume of this sort of traffic is currently quite low.
